Media Protection (MP): Why Your Storage & Transport of Data Could Make or Break Your Contract
When a $10 USB Costs a $10 Million Contract
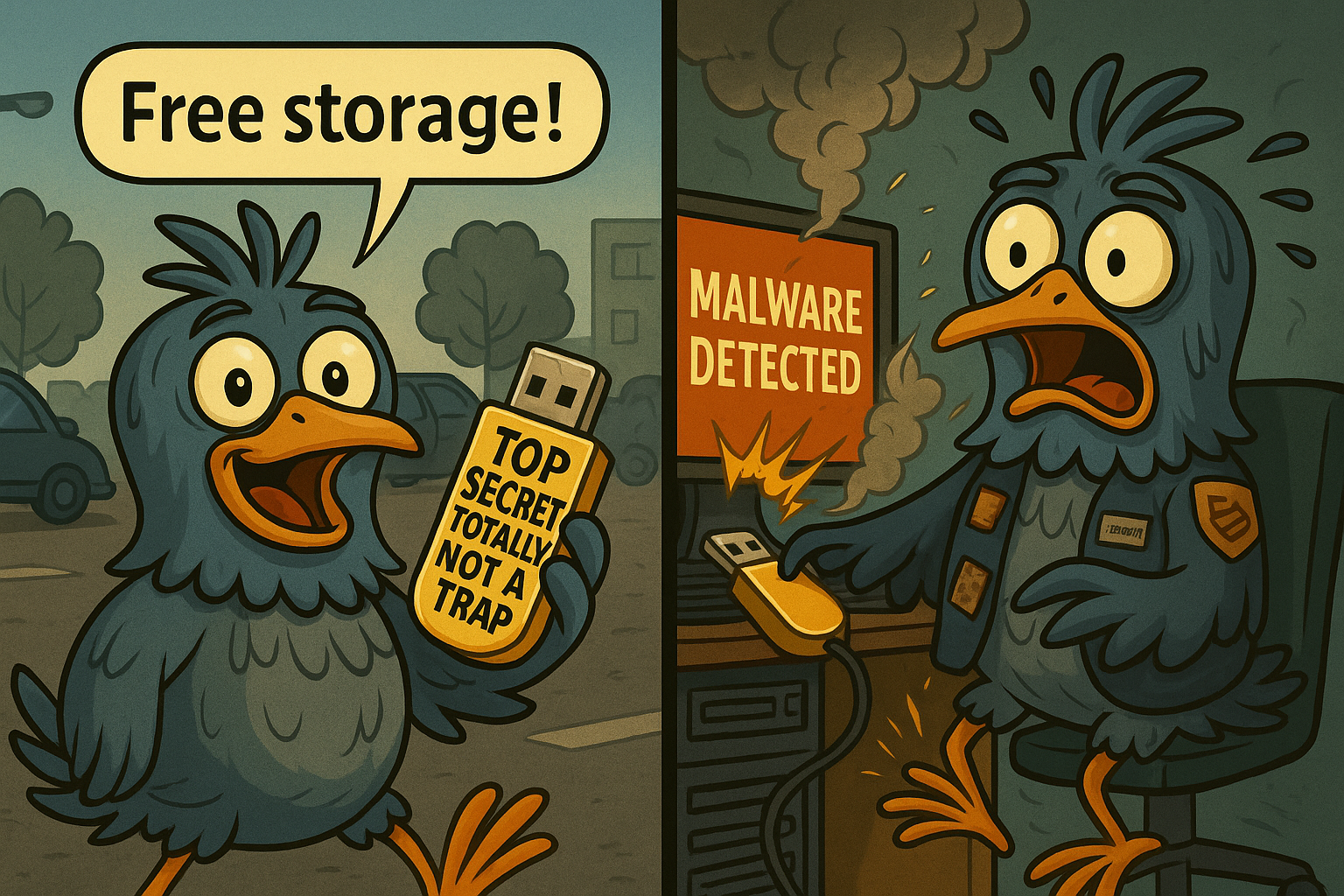
Imagine this: It’s 6:30 p.m. on a Friday, and an engineer from a mid-sized defense subcontractor, let’s call them Acme AeroSolutions, is wrapping up a week of work on a new aeronautical component for a DoD prime contractor. They pull a USB-stick from their bag – containing schematics with Controlled Unclassified Information (CUI) – and plug it into their laptop. As they sign off for the weekend, the USB drive is left on the desk overnight. Meanwhile, a cleaning crew empties the trash: the drive ends up in a bin, eventually in the dumpster.
Two weeks later, the prime contractor learns someone found the drive and observed the files. The DoD halts contracting activities while investigations unfold. Acme AeroSolutions has not only lost the contract but now faces remediation obligations, reputational damage, and increased insurance premiums.
This isn’t just hypothetical – it’s exactly the kind of scenario the CMMC 2.0 Media Protection (MP) family aims to prevent. If you’re an SMB in the U.S. defense industrial base (DIB), you cannot afford to treat media protection as an after-thought or checkbox exercise.
In this article we’ll walk through what Media Protection means under CMMC 2.0 in plain business leader language. We will show what auditors are looking for, translate it into business value, explain where most companies fail, and give you a clear roadmap. This includes a Starting Point you can implement today and a “NEX Level” you can grow into for real resilience and competitive advantage.
What Meeting the Objectives Might Look Like
For your SMB (handling CUI under DoD contracts) aiming for CMMC Level 2 (or self-attestation appropriate for your contract), this is what an auditor or assessor will expect to see regarding the Media Protection control family. In simple language:
- You have identified all media (digital and physical) that contain CUI – paper, USB drives, external hard drives, backup tapes, cloud storage, even devices like printers/copiers with temp storage.
- You physically lock, store or otherwise secure that media when not in use – locked cabinets, restricted rooms, logical access controls.
- You limit access to that media to authorized users only – both logically (permissions, encryption) and physically (who can open the cabinet).
- You sanitize or destroy media before disposal or reuse – so if you throw away a hard drive, it’s wiped or shredded, not just tossed.
- You mark media containing CUI with the proper labels and distribution limitations – so it’s clear it’s sensitive.
- You control and track media during transport outside controlled areas – if you hand off a USB to a courier, or a laptop goes off-site, you have chain-of-custody or encryption in place.
- You apply cryptographic controls to digital media during transport or storage – unless physical safeguards suffice.
- You restrict or prohibit removable media (USB sticks, external drives) when appropriate – especially if they don’t have an identifiable owner.
- You protect backup media containing CUI – treat your backups like primary assets, secure them, encrypt them, control access.
In short: Media Protection isn’t just about software… it touches physical assets, user behavior, process, and accountability. If you can show documented policy + implementation + ongoing review of these bullet points, you’re covering your auditor’s expectations for MP at Level 2.
Why It Matters: Small Devices, Big Consequences
Media Protection isn’t just another CMMC checkbox… it’s the difference between being trusted and being sidelined. Every file, drive, and backup that contains Controlled Unclassified Information (CUI) represents both a business asset and a potential liability. When that data is lost, stolen, or mishandled, the fallout doesn’t just hit IT – it hits contracts, customers, and credibility.
For small and mid-sized defense contractors, the margin for error is slim. A single unencrypted USB or misplaced backup can trigger an investigation, suspend a project, or cut you off from future opportunities with a prime or the DoD. But when you treat media protection as a core business process – not an afterthought – you turn compliance into resilience. You demonstrate reliability, safeguard your operational continuity, and earn the confidence that keeps contracts flowing.
- Contract eligibility & continuity: If you can’t demonstrate to the Department of Defense or a prime contractor that you handle CUI properly, you may be disqualified from bidding – or worse, have an existing contract suspended. Media breaches or loss of CUI can trigger contract termination or suspension.
- Reputation & trust: Your reputation within the defense industrial base is fragile. A lost USB with CUI may not show up in headlines, but for a prime, it is a red flag: “If you lost it, can you really handle our next program?” Good media protection demonstrates you are a trusted partner, not a liability.
- Risk of data breach & intellectual property loss: Data sitting on unprotected media is like cash in an unlocked vault. Whether it’s design specs, engineering drawings, or contract docs, if an adversary gets access to your media, the downstream cost (remediation, remediation of primes, insurance hikes, litigation) can far exceed the control cost.
- Operational resilience: If you avoid a breach, weak media controls create operational risk: lost backup tapes lead to recovery failures; misplaced USBs result in urgent incident response and forensic costs; unclear media inventories cause audit findings that cost time and money.
- Competitive advantage: Companies that “go beyond the minimum” win contracts faster and with fewer compliance hoops. If you treat media protection as a maturity practice, rather than a checkbox, be able to move faster, bid more confidently, and spend less time fixing audit deficiencies.
Bottom line: Media protection is not “IT’s problem only” – it’s an operations and business continuity problem. Protecting your media means protecting your contract pipeline, your team’s time, your reputation, and your bottom line.
Where Most Companies Slip Up
Even when they intend well, many SMBs in the DIB stumble on media protection in predictable ways. Here are the common pitfalls:
- Under-inventorying media: They think only USB sticks matter. They forget printers, copiers, cloud storage, laptops, backup tapes. Without a full media inventory, they can’t secure or account for all assets.
- Assuming digital = safe: They assume “cloud” or “network share” means secure and skip physical protections or device encryption. But the media still needs securing, tracking, labeling.
- Loose transport controls: A technician takes a backup to home office, a USB is mailed, a drive is shipped without chain of custody or encryption. Then the paper trail is missing.
- Poor disposal/sanitization: Drives or media are “formatted” and reused, not wiped to DoD/NIST standards. Old copies remain accessible.
- No removable media policy: USB sticks multiply, employees plug in personal devices, ownership chain breaks, devices roam uncontrolled.
- Backup neglect: Backups treated like casual copies… stored in unlocked cabinets, unencrypted, on portable media without controls. Then one incident and it becomes major.
- Labeling & handling inconsistencies: Media containing CUI not marked or handled like normal files, causing human error or misrouting.
- Documentation gap: Policies exist but no proof of enforcement: no checkout logs, no inventory updates, no verification of transport chain. Auditor sees policy but no evidence.
Awareness of these slip-ups helps you avoid them – which is the goal of our “How to Start Strong (and Grow Stronger)” section next.
How to Start Strong (and Grow Stronger)
Getting Media Protection right starts with visibility and consistency. You don’t need expensive tools – just clear processes for how media is created, stored, transferred, and destroyed. Start small, stay disciplined, and build from a foundation of control you can actually sustain. Here’s a straightforward two-tiered approach for your business…
A Starting Point: The Minimum to Meet Compliance
These are relatively low-cost, practical actions you can implement fairly quickly to cover the basics of MP in CMMC 2.0:
- Media inventory: Create a spreadsheet (or tool) listing all media types containing CUI in your organization: USBs, external drives, laptops, backups, cloud shares, paper documents, printers. Define the responsible owner for each.
- Secure storage: For physical media, ensure locked cabinets or rooms when not in use; for digital media, ensure device encryption (e.g., BitLocker), access control, and network share permissions.
- Access control: Define who can use which media, and ensure permissions/logical access reflect that. Limit removable media use to authorized personnel.
- Sanitization/disposal process: Define procedures for wiping media before reuse or disposal; maintain logs of disposal.
- Transport controls: If media leaves controlled space (e.g., off-site backup, courier), ensure encryption or locked container plus check-out/check-in logs.
- Labeling: Ensure media containing CUI is marked per your policy – both digital (file headers, folder labels) and physical (stickers, clear notation).
- Backups: Realize backups containing CUI are equally sensitive – ensure they are encrypted, access-controlled, and stored securely.
- Documentation: Assemble a brief policy/procedure for media protection covering the above points, and maintain logs/proof of implementation (inventory entries, disposal logs, transport logs).
If you implement these basics, you’ll be in good shape to satisfy an auditor’s Level 2 assessment of the Media Protection family.
The NEX Level: Enhanced practices that create resilience and competitive edge
Once you’ve got the basics operating, you can raise your posture to a maturity level that helps you win contracts and sustain your operations with less risk:
- Media usage tracking tool: Implement software or devices that track removable media usage (who used which device when), integrating with your asset monitoring and SIEM records.
- Automated encryption and DLP (Data Loss Prevention): Ensure removable drives automatically enforce encryption, and policies prevent unapproved media from being used; digital file tags trigger DLP alerts.
- Chain-of-custody management for media transport: Formalized check-out/check-in systems with electronic signature, GPS tracking for courier shipments, tamper-evident containers for off-site media.
- Media lifecycle managements: From acquisition → usage → archiving → disposal, have documented lifecycle workflows with periodic reviews/ audits, and retire media assets proactively.
- Secure decommissioning of physical media devices: Use certified destruction, and maintain certificates of destruction; include inspection of printers/copiers, backup tapes, deproxying cloud storage.
- Segmentation & access zoning: Physically segregate storage areas for CUI media vs external media; logical segmentation ensures media devices cannot be used in untrusted zones (for example, USB ports disabled on production systems).
- Incident scenario exercises: Run periodic “dropped media” drills: simulate loss of a USB with CUI, walk through process, identify gaps in response and forensics, and improve controls accordingly.
- Metrics & continuous improvement: Track key metrics (e.g., number of unauthorized media incidents, time to disposal, number of removable media devices in use, audit findings), and present to leadership. Use dashboards to drive improvement.
By climbing to the NEX Level, your media protection program becomes not just audit-worthy but business-enabling… you reduce waste, accelerate contracts, and demonstrate to prime contractors that you’re a mature partner, not just “compliant”.
The “Lock-Box” Lesson
Think of your business as a warehouse for prototypes and documentation. The “media” in question – USB drives, external drives, printed drawings – are like physical blueprints and models. Now imagine you place all your blueprints inside a single clear glass box on the showroom floor with no lock. Anyone can reach in and flip through them. That’s what leaving unprotected media is like.
Now imagine instead… you move that box into a locked vault and only certain employees have badges to open it. Every time a document comes out someone signs it and when one is obsolete you shred it in front of a witness. Finally, when a copy goes off-site it’s in a tamper-sealed courier container with GPS tracking and a chain-of-custody log. That’s the NEX Level.
Takeaway: If you wouldn’t leave your prototypes on the showroom floor for a rival to grab, don’t leave your media unprotected for a cyber-thief to swipe.
Helpful Resources
Media protection doesn’t have to be complicated – but it does require consistency. The right tools, training, and references can make that consistency repeatable across your organization. Whether you’re building your first CMMC-compliant process or strengthening existing controls, the resources below can help you translate requirements into daily practice.
We’ve grouped them into four categories: Framework & Standards for understanding what’s required, Free Training & Tools to help you build capability at low cost, Paid Solutions that automate and scale protection, and CyberNEX Resources that guide you every step of the way – including our CMMC Decoded: Media Protection one-pager for quick reference.
Framework & Standards
- DoD CMMC Resources – Official documentation from the DoD covering CMMC Model v2.0.
- NIST SP 800-171 Rev. 2 – Full text from NIST, the source standard that CMMC maps to.
Free Resources
- Webinar: CMMC 3.8: Media Protection by Ntiva – covers practical implementation and common mistakes. They also have a great blog on MP.
- MP: Safeguarding Sensitive Data & Storage Devices by Agile IT – clear breakdown of each MP control.
Paid Resources
- Forcepoint DLP – risk-adaptive DLP that scales across endpoints, cloud, and network channels; strong for organizations that need behavioral analytics to reduce false positives while enforcing removable-media policies.
- CYYNC – A centralized system to plan and track evidence collection, conduct and document self-assessments, manage POA&M items through remediation, and maintain a continuous audit trail.
- Iron Mountain Secure Shredding & Media Destruction – certified destruction services and Certificates of Destruction for paper and electronic media. Ideal for MP disposal/sanitization controls and for providing auditable proof to primes/assessors.
- Rubrik / Cohesity (data management & immutable backups) – platforms that provide hardened backup stores, encryption, and tamper resistance – useful for MP controls that call out backup media protection. (See vendor sites for solution details.)
- ManageEngine Device Control Plus – lower-cost device control option for locking/monitoring removable devices and generating usage logs – good fit for budget-conscious SMBs that still need auditable controls.
CyberNEX Resources
- CMMC Decoded: Media Protection Reference Sheet – A concise one-page guide for defense contractors that outlines the MP control family, explains why it matters, highlights examples of evidence auditors might expect, provides quick-win actions to get started, and includes links to available resources.
- CyberNEX Blog Archive – Explore all 14 CMMC control families with in-depth explainers, practical recommendations, and actionable insights tailored to defense contractors.
Take the NEXt Step
Compliance isn’t the finish line – it’s the foundation. Media Protection is one of those control families that proves whether your organization truly handles data with discipline. And discipline builds trust… the kind that keeps DoD contracts coming, primes confident in your performance, and customers returning year after year.
At CyberNEX, we help small and mid-sized defense contractors move from “checking the box” to building real resilience. Our team has walked hundreds of businesses through practical steps to safeguard data – whether that means tightening removable media policies, improving encryption, or creating traceable, auditable backup procedures. We speak the language of operations, not theory.
👉 Get clarity on your compliance gaps and a clear plan forward. Book a Discovery Session with our experts today.
Not ready to chat yet?
→ Learn more about our CMMC Readiness Assessments
→ Subscribe to NEX Level Newsletter
FAQs
1. What exactly does the Media Protection (MP) control family require under CMMC 2.0?
It requires you to protect all system media (paper and digital) containing Controlled Unclassified Information (CUI) through controls around storage, access, sanitization/disposal, labeling, transport, removable media usage, backups and encryption.
2. Does media protection just mean no USB sticks allowed?
No – while restricting removable media is one important practice (e.g., USB drives>), media protection is far broader. It includes physical media (paper), digital media (hard drives, cloud storage), backup media, labeling, transport, encryption, access control, and more.
3. I’m a small contractor with limited budget – can I still meet MP requirements without huge investment?
Absolutely. The “Starting Point” actions (inventory, locked cabinets, device encryption, labeled media, documented disposal, basic transport logs) cover most audit expectations. You don’t need enterprise-grade tooling right away – just consistent process and accountability. Over time you can grow into the NEX Level.
4. If I focus on media protection only, am I fully compliant with CMMC 2.0?
No. Media Protection is just one control family of many under CMMC 2.0. You’ll also need to address other families (Access Control, Audit & Accountability, System & Communication Protection, etc.). But media protection is often overlooked and yet critical; doing it well gives you a strong foundation and credibility.
5. How often should we review or update our media protection process?
At minimum annually… and whenever there’s a significant change (new contractor, new contract, new type of media, new off-site use case). For higher maturity (NEX Level) status, consider quarterly reviews, periodic drills, and metrics tracking to drive continuous improvement.